The EU Digital Identity Wallet, or EUDI for short, will be a new way for Europeans to prove who they are when accessing digital services. It will be a smartphone app that enables citizens, residents and businesses to identify themselves, safely request, store and share important digital documents, authorise payments and electronically sign or seal documents. Each member state is required to adopt at least one wallet application by the end of 2026. In Finland, the digital wallet is being built by the Digital and Population Data Services Agency.
The wallets are one element of the broader EU Digital Identity Framework, which is transforming the way identity is managed in a digital society. The plastic cards and paper documents carried in a physical wallet will be replaced by a model that enables users to control their own data by deciding what they store and who they share it with. Initially, the wallet will be used for strong electronic identification and digital signatures, but its features will be expanded in phases to also include a wider set of credentials, such as driving licences, degree certificates and other documents that may be needed when dealing with public or private services.
In the first phase, the Finnish wallet will include a digital proof of identity, which will initially be valid only nationally. This basic identity attribute forms the foundation of digital service use and provides the basis for other documents that may later be added to the wallet.
From a data protection perspective, the implementation model chosen by Finland is well grounded. The wallet app will be free of charge and voluntary to use, and it will not be built on a centralised national data repository. The users remain in full control of their own data. This reflects the European principle of privacy by design and sets the solution apart from many earlier models.
The EUDI Wallet is eventually designed to function throughout the EU. The revised eIDAS Regulation makes digital identity genuinely Union-wide and harmonises identification across member states. Digital identity will no longer be confined to national systems but will form a common European infrastructure for identification.
The useful features of the digital wallet also inevitably make it an attractive target for criminals.
This is often the point where the discussion stops. Enhanced security, strong identification and high technical requirements are highlighted, but much less attention is paid to the flipside – the fact that these same features also inevitably make the digital wallet an attractive target for criminals.
It should surprise no one that fraudsters would be interested in gaining access to digital identity wallets. After all, the wallet is a treasure trove of critical personal data and acts as a gateway to a wide range of services. For criminals, the potential value is obvious. This does not, however, indicate that the technology has failed; on the contrary, it is a direct consequence of how important a role it plays. Criminals typically zero in on targets where trust, value and influence intersect.
Talking about security in a one-sided manner is risky. Constantly emphasising the official status and technical safety of the wallet may create a false sense of security among users and make them more likely to trust requests received through the wallet app without questioning their legitimacy. The wallet app does not disclose why the request has been sent, only who made it and what information they are asking for. When risks are not discussed openly enough, users rely on the perceived safety of the solution and let their guard down. The ultimate decision and liability remain with the individual user.
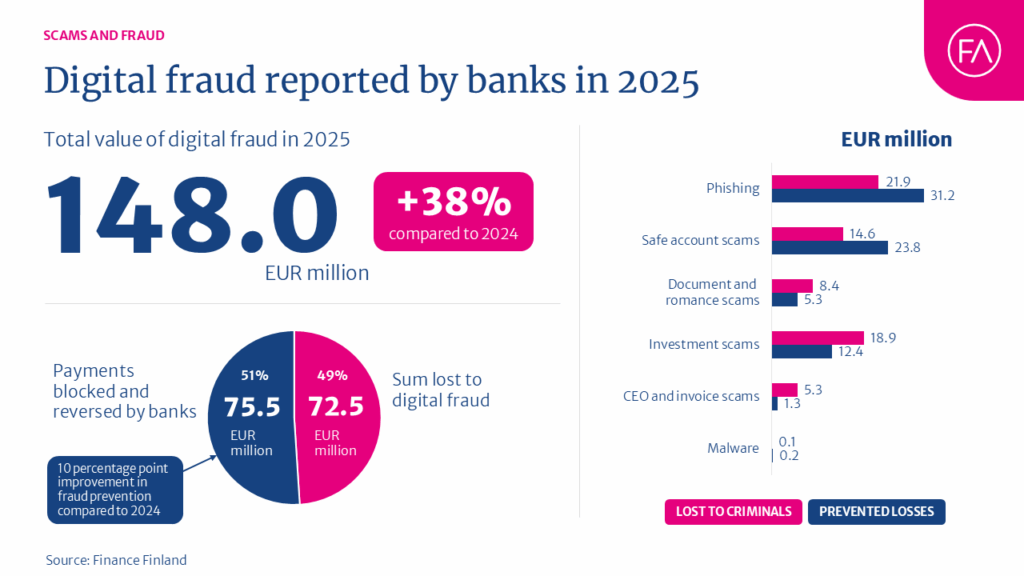
The same pattern is already visible in the broader evolution of fraud. In 2025, scams based on social engineering already accounted for around 60% of fraud cases reported by banks. Rather than breaking into systems directly, criminals increasingly focus on manipulating people into making mistakes themselves.
The rollout phase of the digital wallet is particularly vulnerable. Once the wallets are launched and their features gradually expand during 2027, uncertainty creates opportunities that criminals are ready to seize. We can expect a wave of fake wallets, fraudulent download links and scam messages during this phase.
Over time, the risks will also become more sophisticated. Likely scenarios include wallet takeovers, use of malware and remote-access tools, identity theft and even breaches in the systems of certified actors. While certification and supervision reduce risks, they do not eliminate them. If a trusted service provider is compromised, fraudsters gain a powerful channel for sending seemingly legitimate requests to large numbers of users.
None of this is an argument against the digital identity wallet. It is, however, a strong argument for having a realistic discussion about risks early on, rather than waiting until the first large-scale abuses have already occurred.
At its core, the digital identity wallet is an infrastructure. It has the potential to improve security and mitigate many existing risks, but it does not make the entire ecosystem invulnerable. Risks will emerge from the interplay between the wallet, the services built on top of it, the processes behind them and the people using them. Trust is the greatest strength of the system – and at the same time, its greatest vulnerability, unless it is balanced by awareness.
Security is not created by sweeping fraud risks under the carpet. It is created by acknowledging those risks and preparing for them in good time.
Sira Nieminen
Fraud Prevention Specialist
Finance Finland